A Good Cybersecurity Marketing Lead is Hard to Find

Intent data has a reputation problem, especially with cybersecurity marketers
Many marketing intent data providers in the cybersecurity space have made bold promises about lead quality—only to deliver vague signals and questionable accuracy.
And many marketers who use their services are not satisfied with the results, claiming they are not getting any added benefits. Here’s what we’ve heard about failed intent data programs/providers.
“It’s just another spreadsheet.”
“They forgot about us as soon as they delivered the leads.”
“These contacts aren’t even in the cybersecurity ecosystem.”
The reality is that you can’t claim to know which buyers are ready to buy unless you have meaningful data to support their behavior. Cybersecurity sales cycles are complex. You need to monitor the buyer content journey, and confirm it’s aligned to pain points your solution can address.
Contact level intelligence comes with built-in reputation
A key shift is moving away from proxies and toward observed, verifiable contact level intelligence. That means tracking real engagement—downloads, repeat visits, and multi-touch activity—across trusted content environments. This is key.
Avoid providers with untrusted data ecosystems and hidden lead sources
Here’s what a trusted cybersecurity content ecosystem should provide:
Multiple downloads across a variety of assets. This reveals not just interest, but depth—indicating what stage the buyer is in and what topics resonate most. These behavioral insights can uncover tangential solution narratives, giving sales teams richer context to craft more relevant, high-impact outreach.
Repeat engagement signals that demonstrate sustained interest. This helps distinguish casual browsers from serious buyers.
A defined time scope—such as activity within the past 30 or 60 days—ensures outreach is timely and focused on prospects who are actively evaluating solutions, improving conversion potential.
Making sense of non-linear buyer journeys
Multi-touch activity is a cornerstone of modern digital marketing because it reflects a more realistic, non-linear buyer journey. Within trusted content ecosystem, you get repeat visitors who rely on the content to make more informed decisions on their own terms without a sales rep trying to pitch them without always taking the time to listen carefully
Buyers typically engage with several types of content—whitepapers, webinars, emails, social posts—before having enough context to make a decision. Here are some data points and insights that underscore its importance:
- According to Salesforce, it takes multiple personalized touchpoints to generate a viable sales lead.
- A report by Demand Gen found that 76% of B2B buyers consume three or more pieces of content before engaging with a sales rep.
- Gartner research shows that buying groups spend 45% of their time researching independently online, meaning multi-channel engagement is critical for staying top of mind.
Having detailed data on multi-touch activity is the next best thing to lengthy conversations with your buyer to understand their unique needs.
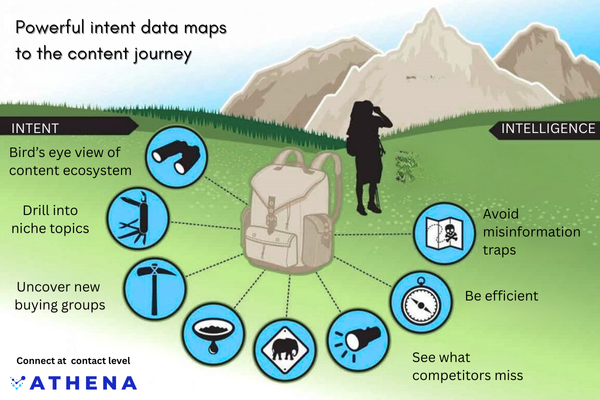
Contact level intellignce provides the necessary toolkit for cybersecurity marketing and sales team to understand buyer's true interests and meet them where they are.
When data reflects authentic buyer interest, marketers can build marketing programs that actually convert. Fixing intent data’s reputation won’t happen overnight, but it starts with being honest about what works.
If you would like to learn more about how intent data can make you top of funnel more manageable, check out our article on
Why Cybersecurity Marketers Need Better Intent Data to Survive
By prioritizing quality over volume and aligning data with real human behavior, we can restore confidence and drive better results across the funnel. Trust, once rebuilt, becomes a force multiplier.
