10 Ways Paid Campaigns Pressure-Test Cybersecurity Messaging

Cybersecurity marketing has a dirty secret: most messaging decisions are based on opinion, not data. Paid campaigns fix that. Instead of arguing about which message works, you can run fast experiments and let the market tell you the answer in a few weeks. Research backs this up: according to Nielsen, 76% of marketing leaders say they rely on gut instinct over data when making messaging decisions.
That’s a costly habit. In cybersecurity specifically, where buying cycles are long, stakeholders are numerous, and trust is everything, guessing wrong doesn’t just waste budget—it actively erodes credibility. Paid campaigns give you a feedback loop that internal debate never can. A modest $2,000–$5,000 test budget can produce statistically meaningful signal within three to four weeks.
The discipline isn’t about spending more. It’s about learning faster than your competitors and compounding those insights across every channel you own. Here are 10 ways I use paid campaigns to pressure-test cybersecurity messaging before committing to it.
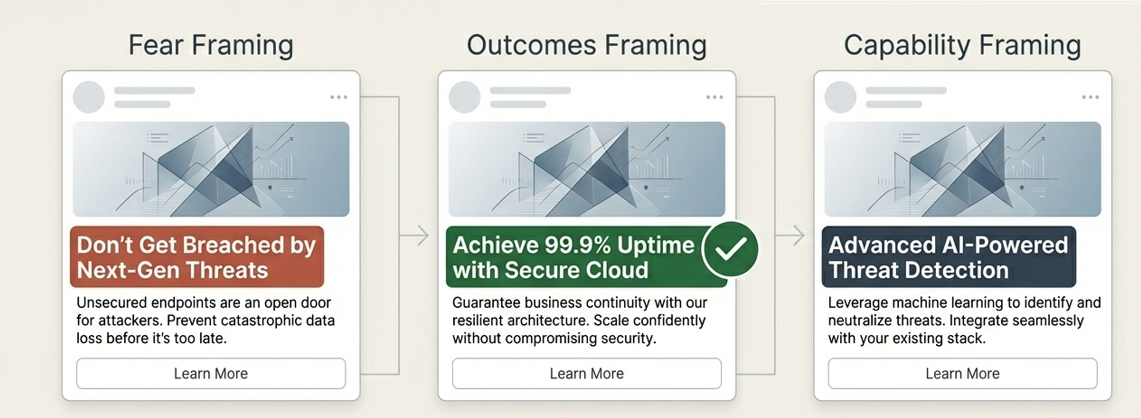
1. A/B Test Headlines to See Which Emotion Actually Works
Cybersecurity marketers love fear-based messaging, but buyers don’t always respond to it. Run identical ads with different headline frames—fear, outcomes, or capability—and see which gets the highest click-through rate. The winning headline often reveals the real pressure driving your buyer’s decisions. A 2023 Gartner study found that B2B technology buyers are 1.5x more likely to engage with content that emphasizes business outcomes over technical capabilities—yet the majority of cybersecurity ads still lead with threat language. Fear works when the threat feels imminent and personal; it backfires when buyers are fatigued or already desensitized. In OT and industrial security, where audiences have lived through years of “the sky is falling” headlines, outcome-framing like “keep production running” consistently outperforms fear-framing in head-to-head tests. Run at least three variants, let each accumulate 500+ impressions before drawing conclusions, and resist the urge to call a winner too early.
2. Test Different Buyer Pain Points
Most vendors assume they know what their customers are worried about. Create separate campaigns centered on different fears—compliance risk, downtime, reputational damage, or skills gaps—and see which one converts. The winner tells you what your audience is actually losing sleep over. You may be surprised: a Ponemon Institute survey found that OT security professionals rank unplanned downtime as their #1 concern—above regulatory fines and above data breach liability. Yet the majority of industrial cybersecurity vendors lead with compliance messaging, because that’s what resonates with legal and procurement, not with the operational teams actually making vendor recommendations. Running pain-point segmented campaigns surfaces this disconnect quickly. Budget $500–$1,000 per pain-point variant, use the same creative format across all of them to isolate the variable, and measure not just clicks but downstream conversion to demo or content download. The gap between assumed and actual pain points is often where your best positioning lives.
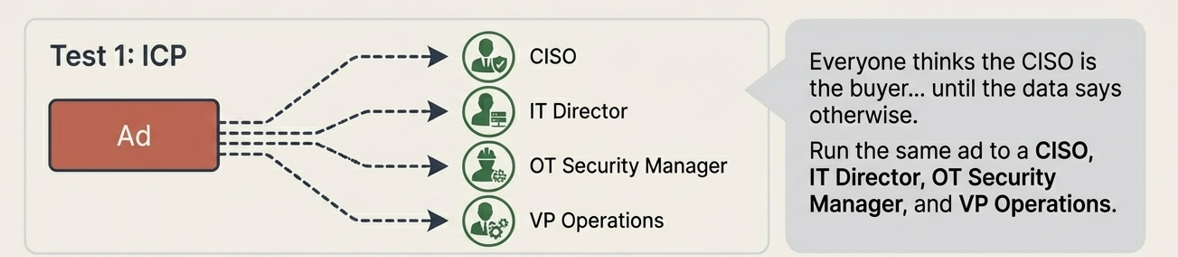
3. Use LinkedIn to Pressure-Test Your ICP
Everyone thinks the CISO is the buyer… until the data says otherwise. Run the same ad to different roles—CISO, IT Director, OT Security Manager, VP Operations—and compare results. You might discover the real buyer isn’t who your sales deck thinks it is. LinkedIn’s targeting granularity makes it uniquely suited for this test. According to LinkedIn’s own B2B Institute research, the average enterprise technology purchase involves 6 to 10 stakeholders, and the person who initiates vendor research is often not the budget holder. In industrial cybersecurity, engineering and operations titles frequently drive the shortlist before procurement or the C-suite ever gets involved. A well-structured ICP test on LinkedIn—same ad creative, same landing page, different audience segments—can reveal which roles engage, which roles convert, and which roles amplify your content to others. That data is worth more than any persona document built in a conference room.
4. Steal Your Buyers’ Language from Google
Cybersecurity marketers often describe solutions using internal product language. Buyers search using totally different words. Run broad match search campaigns and check the Search Terms Report—it’s basically a cheat sheet for how your customers actually talk. The semantic gap between vendor language and buyer language in cybersecurity is well-documented. Vendors write about “unified OT/IT visibility platforms”; buyers search for “how to see what’s on my plant network.” Google’s Search Terms Report surfaces the actual queries triggering your ads, giving you unfiltered, unmediated access to buyer vocabulary at the moment of need. Tools like SparkToro and SEMrush can supplement this, but nothing beats live search data from an active campaign. Harvest this language and feed it back into your landing pages, sales decks, and organic content. Copy that mirrors how buyers already think reduces cognitive friction and almost always improves conversion rates.

5. Test Specific Claims vs. Vague Promises
“Protect your environment” sounds nice but says nothing. Compare that to something concrete like “Reduce OT attack surface in 30 days.” Specific claims almost always win because they give buyers something measurable to believe. The research on specificity in B2B copy is consistent: MarketingExperiments has repeatedly shown that concrete, falsifiable claims outperform abstract benefit statements by 20–40% on landing page conversion rates. In cybersecurity, where skepticism is high and vendor claims are notoriously difficult to verify, specificity signals credibility. A claim with a number—a timeframe, a percentage, a benchmark—implies that someone measured something. That implied rigor builds trust even before a buyer has spoken to your sales team. The discipline here is forcing your team to actually know what you can prove. If you can’t substantiate a specific claim, that’s a product marketing problem worth solving before it becomes a sales problem.
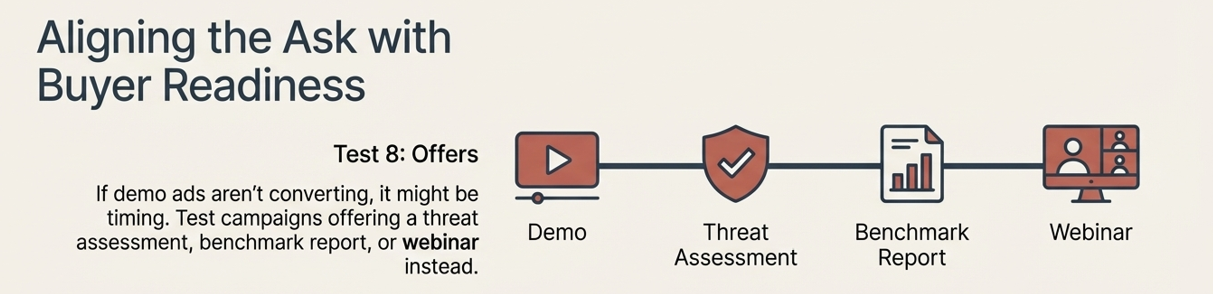
6. Test Offers to Reveal Where Buyers Are in the Journey
If your demo ads aren’t converting, it might not be your demo—it might be timing. Try running campaigns offering a threat assessment, benchmark report, or webinar instead. The offer that converts tells you how ready your audience actually is to buy. Demand Gen Report’s 2023 B2B Buyer Survey found that 62% of buyers engage with three to seven pieces of content before speaking to a vendor. Pushing a demo to a cold audience is like proposing on a first date. Testing softer offers—educational content, diagnostic tools, peer benchmarks—helps you understand where the majority of your addressable market actually sits in the funnel at any given time. In industrial cybersecurity, where procurement cycles routinely run 12–18 months, the ability to capture and nurture early-stage buyers is a significant competitive advantage. The offer test is also a proxy for audience intent: what someone is willing to give their email for tells you a lot about what they’re trying to solve right now.
7. Use Retargeting to Test Your Follow-Up Message
Most visitors won’t convert on the first visit, and that’s normal. Retargeting ads give you a second chance to figure out what message brings them back. Try brand messaging versus use-case messaging and see which one pulls them deeper into the funnel. Studies consistently show that retargeted ads perform 3–10x better than cold display ads on click-through rate, but most teams run a single retargeting creative and assume the work is done. The smarter play is to treat retargeting as its own messaging experiment. Someone who visited your OT assessment page but didn’t convert—do they respond better to a customer story, a product capability highlight, or a low-friction content offer? Split your retargeting pool by page visited and test different message angles against each segment. This tells you not just what brings people back, but what specific narrative closes the gap between interest and action for each stage of buyer awareness.
8. Test Differentiation Messaging
Sometimes the best message isn’t what you do—it’s what you do differently. Try ads that contrast your approach against the category—for example, “IT security training isn’t built for OT environments.” If the contrast campaign wins, you’ve found a positioning angle worth doubling down on. Category contrast is one of the most underused tools in B2B cybersecurity marketing. When a market is crowded and buyers struggle to differentiate vendors, ads that reframe the category itself cut through the noise more effectively than feature-benefit messaging. Challenger brand research from Bain & Company shows that buyers in saturated markets are more responsive to messages that challenge their existing assumptions than to messages that simply reinforce a vendor’s strengths. The key is to name the contrast credibly, not dismissively. “Built for OT, not retrofitted from IT” works because it articulates a real architectural truth—and it invites the buyer to interrogate competitors using your frame, not their own.
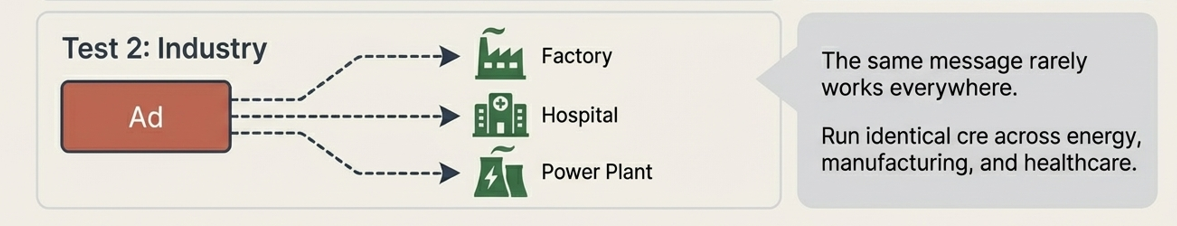
9. Segment Campaigns by Industry
The same cybersecurity message rarely works everywhere. Run the same creative across different industries—energy, manufacturing, healthcare—and watch the results. The verticals that convert best are often where your product naturally resonates. Even when the underlying technology is identical, the regulatory context, threat landscape, and operational priorities differ dramatically across verticals. A message about compliance resonates differently in healthcare (HIPAA, HITECH) than in energy (NERC CIP) than in manufacturing (no federal mandate at all, so ROI-framing tends to win). According to Forrester, 74% of B2B buyers say they expect vendor communications to be personalized to their industry—and only 36% say they regularly receive messaging that meets that bar. Industry segmentation in paid campaigns lets you quickly identify where your generic message is already landing and where it needs to be localized. High performers in one vertical are often strong signals for an industry-specific content or ABM investment.
10. Test Content Ideas Before Writing Them
Writing a 3,000-word blog post only to discover nobody cares is painful. Instead, run a short LinkedIn ad or boosted post presenting the core idea. If it gets strong engagement, congratulations—you just validated your next piece of content. Content production in cybersecurity is expensive when done well—original research, subject matter expert interviews, legal review, design. Spending $150–$300 on a LinkedIn post to test a content thesis before commissioning the full piece is one of the highest-ROI investments a content marketer can make. Engagement rate, comment quality, and share behavior are all leading indicators of organic content performance. BuzzSumo data consistently shows that the top 10% of B2B content earns 90% of shares—meaning the cost of producing content that misses is enormous relative to the cost of a quick validation test. Treat your paid social feed as a continuous content R&D lab, not just a distribution channel.
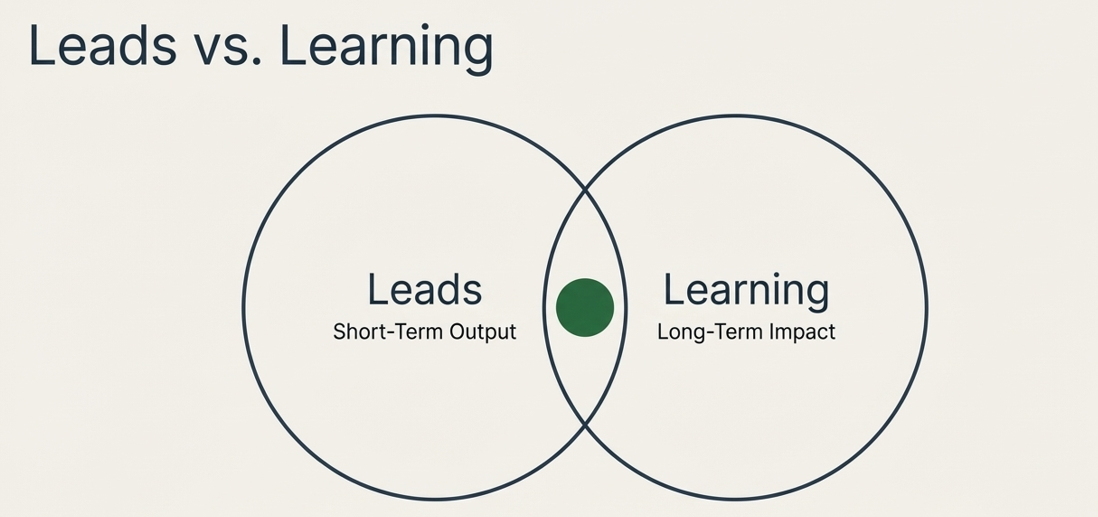
The Real Product of Paid Campaigns
Every paid campaign produces two things: leads and learning. Most marketers focus only on the leads. The smart ones focus on the learning. Because once you figure out the message that truly resonates, everything in your marketing gets easier. The compounding effect is real: brands that systematically test and refine messaging see 20–30% improvements in conversion rates over 12-month periods, according to HubSpot’s State of Marketing report—not because they spent more, but because they stopped guessing. In a category as competitive and trust-dependent as cybersecurity, message-market fit isn’t a nice-to-have. It’s the difference between a pipeline that compounds and a budget that evaporates. Build the testing habit now, and the learning becomes your most defensible asset.